End-to-End Encryption (E2EE) as we generally think of it protects our communications from any third party while it is moving between us and the other user we are communicating with. It’s difficult even for State actors to discern the contents of a truly E2EE communication. That’s why it is so useful, and at the same time, can be so dangerous. True E2EE, at this time, is about as secure as you can get with a communication. If you’re sending the nuclear codes from one person to another, you better make sure your connection is E2EE. In this article, we talk with Graham Nelson-Zutter, of Corvum.io, about the basics of E2EE in video conferencing.
Category Archives: Security
Lately, law offices all over the country have been turning to video conferencing to meet with clients, talk to teammates in their offices, and even attend remote hearings. But with the speedy move to these tools, I’d venture to guess that some of us are outside of our comfort zones, now. That’s okay. These are new paths we’re forging in how we communicate with our clients and others in the legal field. It can, understandably, take some time to acclimate to new methods.
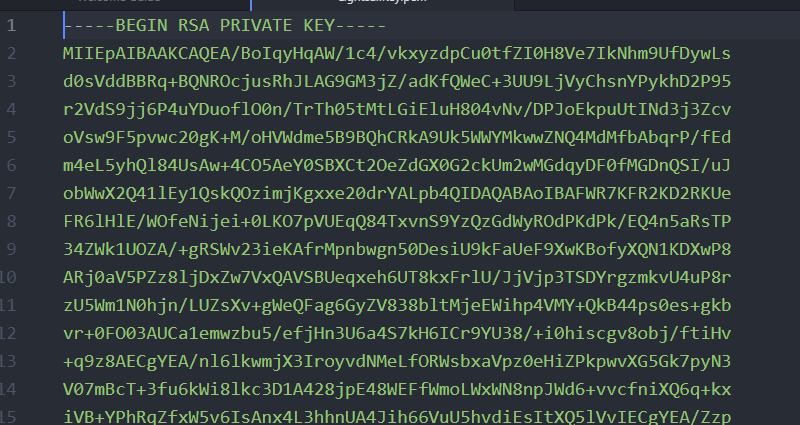
Above is a section of a private key that was previously used to log into a webserver. This is a partial example of asymmetric encryption. Part 1: What Does Encryption Do? As lawyers (and pretty much just as humans who exist in a digital world) we’re given a lot of surface level advice about encryption. […]
Data Back-ups and Due Care Let’s talk about safeguarding client files and how advancements in technology are changing what due care means. First off, let’s not be unreasonable, we, as lawyers, don’t have an obligation to incorporate every single emerging technology into our practices. That’d be overwhelming, and likely wouldn’t be financially beneficial to anyone […]
Basics: As lawyers and legal professionals, most of us understand that we are entrusted with a lot of sensitive information about our clients. And, generally, we know how to protect it. At least in the real world. We have security systems in our offices, locks on our files, and we limit access to certain rooms […]